Analyzing the Power Consumption of Mobile Antivirus Software on Android Devices
November 8, 2015 Shem Radzikowski Comments Off on Analyzing the Power Consumption of Mobile Antivirus Software on Android Devices

With an influx of security bulletins for Android-based devices, I decided to install antivirus software on my Android phone as a precautionary measure. However, the experience was anything but ideal — poor performance and high battery consumption.
While security has a price on any platform, battery powered devices suffer far more because they can only store a finite amount of energy. This prompted me to investigate whether all antivirus apps are created equal when it comes to power consumption — as it turns out, they aren’t.
25% Power Drop after Installing AV
I’m reasonably cautious when it comes to my phone, and for good reason, it holds the keys to my entire digital life. At the slightest suspicion of a compromise, unexplained power drain, or even a misbehaving app, I don’t hesitate in blowing away the device back to its factory (or custom rooted) image.
Android’s market penetration and the popularity of smartphones has greatly increased the spread of mobile malware. Their built-in billing system, along with a stack of personal information and account credentials, render them a highly profitable target or pwn.[1]
Power and Batteries
While mobile phone technology has advanced considerably in recent years, batteries have failed to keep pace Modern smartphones packed with a glut of apps, sensors and big screens are struggling to make it through the day on a single charge.
Even large 4000 mAh batteries find it difficult keeping up with demanding power users. A battery rated with a higher mAh will power a phone for a longer amount of time, given the same usage pattern. The trade-off is that batteries with higher mAh are generally also physically larger and heavier.[2]
From 36 to 27 Hours
I won’t comment as to which vendor solutions I tried, mostly because my tests didn’t follow any scientific methods — I’ll let the experts comment on that in the next section. But I will say that the power drain and sluggishness of my phone was noticeable. Even though I have a modern smartphone with a large 3500 mAh battery, the drop in battery life was far more significant than I expected. Battery life dropped to ~27 hours — considerably lower than the 36 hours I was obtaining prior to installation under normal usage.[3] That’s a 25% drop in battery life, quite a chunk.
What do the Experts Say?
Not satisfied with my own experiences, I turned to some academic papers and found one aptly titled: Powerslave: Analyzing the Energy Consumption of Mobile Antivirus Software. The paper evaluated the energy efficiency of six of the more popular AV tools on the Android platform, and explored whether the energy consumption is correlated to their detection quality.
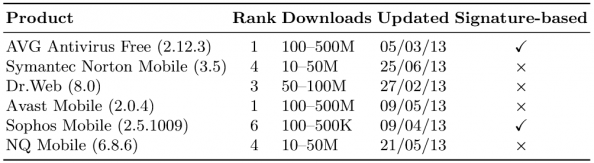
Table 1: List of AV Products Tested. Rank refers to respective rank among the tested AVs based on their downloads in Google Play.
Malware Detection Rates
The relation between energy consumption and detection rate is shown in Table 2. While AVG is the most energy-efficient, it also achieves the lowest detection rate. The most effective AV engine in terms of detecting malicious apps (Norton) is also highly efficient in terms of energy consumption. Specifically, while achieving a 98.8% detection rate, it [Norton] consumes 46.2% — 65% less energy than three of the other AVs.
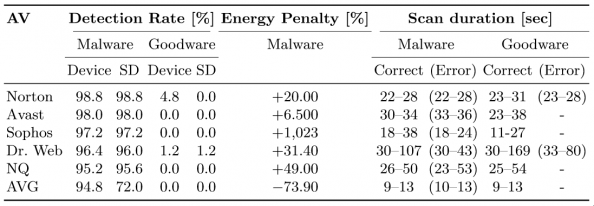
Table 2: Detection outcome for all scanning modes, and duration of the “On Demand” scan. The “Correct” and “Error” columns refer to correct and erroneous labelling by the AV for the apps being scanned. The “Energy Penalty” expresses the percentage of energy wasted due to the AV misclassifying a malicious app as benign.
Sophos exhibits the highest consumption of all, consuming 22.2% more energy than Avast that has the second highest consumption. Compared to the remaining apps, Sophos consumes 53.8% more than NQ, 185% more than Norton, 215% more than Dr. Web, and over 326% more than AVG.
The type of signature-based heuristics employed by the AV can impact certain aspects of its energy consumption. To test this, the researchers altered some of the package names (and thus the file hash) of the malware samples and repeated the scans for all the AVs. Sophos failed to detect a single sample, indicating that the effectiveness of its detection engine relies significantly on signatures which can be trivially evaded, all the while exhibiting the highest energy consumption of all the AVs. AVG is also severely impacted, detecting only 30.2% of the malware samples. As can be seen in Table 1 the remaining AVs were not impacted, and achieved the same detection rate as previously.
Energy Consumed by CPU
The majority of apps installed by users are benign. As such, a significant aspect of the energy consumption of AVs is how they handle such apps. When scanning an app, if one of the heuristics is triggered, the AV can flag the app as malicious and save energy by not executing the remaining heuristics.
Sophos, NQ and Avast consume 64%–169% more energy for goodware. Norton is the most efficient with only a 12.9% increase.
On the other hand, when scanning a benign app, no heuristics will be triggered (unless there is a false positive), resulting in all of them being executed, which will also result in higher energy consumption.
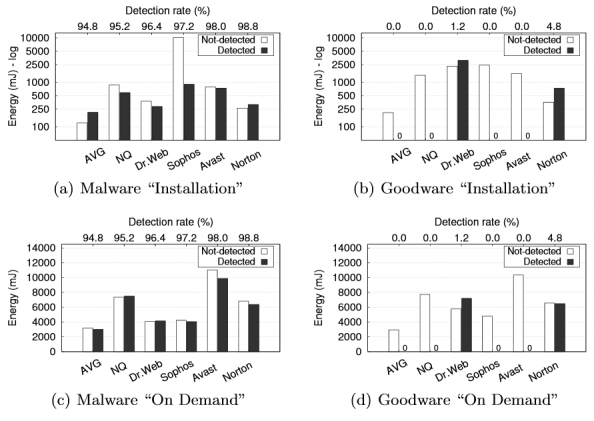
Figure 1: Aggregate energy consumption by CPU during the “Upon Installation” and “On Demand” scan.
Sophos seems to suffer the most in terms of the amount of energy consumed when scanning the malware samples (Table 3), and this was attributed to their internal implementation rather than the malware employing detection or analysis evasion techniques.
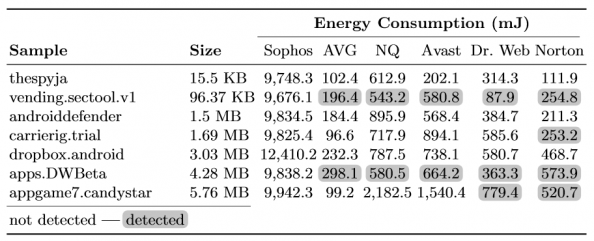
Table 3: Detection outcome and energy consumption of the seven malicious apps not detected by Sophos.
Size does Matter (at least with AV)
The type of heuristics employed may affect the energy consumption of the AV. One would therefore expect larger apps to result in longer scans and increased consumption — but this wasn’t shown to always be the case.
Figure 2 plots the aggregate energy consumed by each AV, and the size of the scanned app. Dr. Web clearly exhibits a strong correlation between the two, and Avast mostly for benign apps. For the remaining AVs size does not seem to be a dominating factor. The lack of correlation may be attributed to fingerprinting techniques that create a compact signature without processing the entire file, or may leverage some indexing technique to speed up matching.
Sophos presents no correlation at all, as there are three clusters of consumption, which remain consistent regardless of app size. The three clusters of consumption “suggest three sets of heuristics and termination of the scan upon detection by a set of heuristics.”
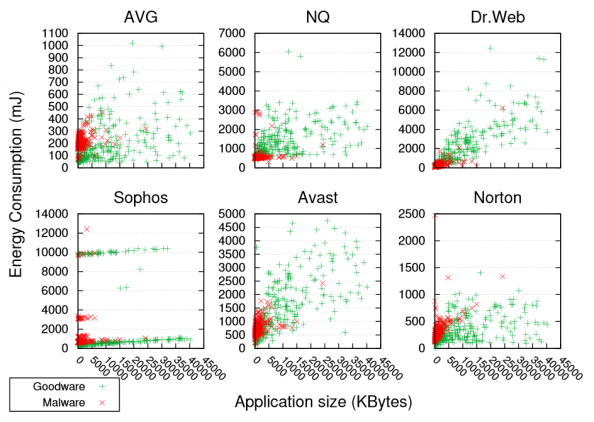
Figure 2: Size and aggregate energy consumption for “Upon Installation” scan.
Conclusion
There are significant differences in CPU energy consumption among different AV products. Based on their findings, the researchers concluded that given the availability of cloud-based scanning, higher detection rates should be possible without sacrificing precious battery life.
Security is generally a cost, and in the case of mobile AVs, the risk is that users may decide to uninstall an AV because it drains too much battery. In other words, the less energy an AV consumes, the more usable it is.
And since security vendors who leverage cloud-based resources are not bound by an “Efficiency vs Accuracy” trade off, they should be able to produce antivirus apps that are highly effective while maintaining modest energy consumption profiles.
So which app to choose? Based on the findings, Norton comes out on top when one wishes to achieve the highest levels of detection while preserving battery life and minimizing false positives.
Footnotes
- Pwn is a slang term derived from the verb own, as meaning to appropriate or to conquer to gain ownership. The term implies domination or humiliation of a rival, used primarily in the Internet-based video game culture to taunt an opponent who has just been soundly defeated (e.g., “You just got pwned!”). ^
- More technically, a higher mAh rating means the (fully-charged) battery can power a device that consumes more power and/or for a longer amount of time before becoming depleted and needing to be re-charged. For example, a battery rated at 1500 mAh can power a device drawing 100 milliamps for 15 hours, or a device drawing 150 milliamps for 10 hours. (In other words, a device using more power will drain the same battery faster.) In that same example, a larger battery, rated 3000 mAh, could power a device drawing 100 milliamps for 30 hours. ^
- “Normal usage” is fairly subjective, but in my case it is mostly limited to responding to a few emails, instant messaging, some web browsing, eBook reading and calls. I have an Acer Liquid E700, 5″ screen, triple-sim with a 3500 mAh battery. http://www.gsmarena.com/acer_liquid_e700-6420.php ^
Bibliography
Related
Android, AV, Avast, AVG, Battery, Dr Web, Energy, Malware, Norton, NQ, Power, Security, Sophos, Symantec Security
Subscribe
Subscribe and receive email notifications the moment Dr.Shem publishes a new post.
Our Sponsors
Recent Posts
- Dublin’s Breaking Point: Riots Expose Ireland’s Immigration Crisis
- Ireland’s Immigration Crisis: A Nation Overwhelmed
- My Journey with Ropes: Scaling New Heights
- Climbing Mountains in and Around Pokhara: An Adventure Beyond the Summits
- A Nomad’s Notebook: Charting My Path Across Continents
- From Pierogi to Pavlova: My Transcontinental Childhood
- Riding Through History: A Personal Journey on the Irish Rail System
- Above the Azure: Discovering the Thrills of Paragliding in Malta
- Immersed in Nature: A First-hand Experience of Hiking in Wicklow
- My Emerald Isle: Why Ireland is the Epitome of Home
- Life in Boulder Colorado: A Quick Guide to Boulderites’ Lifestyle, Culture, and Values
- Rekindling a 25-Year-Old Friendship: A Journey Through Time
- The Spirit of Ireland: A Brief History of Irish Whiskey
- Comparison of Firearm Purchase Procedures in California vs Texas
- First impressions on Austin, Texas and its Tech Scene
- Buying a Gun in California – Not as Easy as it Sounds
- Biometric Hype: A Risky Proposition for Fingerprint and Iris Scanners
- Temple Bar: A Great Place to Live, for the Deaf Insomniacs
- Zero Trust and The Mutating Threat Landscape
- CyberSecurity: Expanded Look at the APT Life Cycle and Mitigation
- Mentors: The Priceless Few and Lessons Learned
- Selected by Hackin9 and eForensics Magazines as a Contributing Cybersecurity Expert
- Notes from the Cloud Security Alliance (CSA) Congress EMEA 2015
- Analyzing the Power Consumption of Mobile Antivirus Software on Android Devices
- Poorly Configured Proxies Leaking Information through “X-Forwarded” and “Via” HTTP Request Headers
- CyberSecurity: A Case Study of the Need for Change
- Cyberconfusion: Cyber Security, Cyber-Security or Cybersecurity?
- CyberSecurity: Origins of the Advanced Persistent Threat (APT)
- A Newcomer’s Take on Dublin Town — First Impressions
- Crypto Wars and Messaging: How Secure are Skype and WhatsApp?
- Reduced Cognitive Performance: Open-Plan Offices, Noise and Collaboration
- First Impressions on Working with Huawei’s European Research Center (ERC)
- Lessons I’ve Learnt from various Relationships
- Money and Friends Don’t Always Mix
- X-Pyr 2014: My Annotated Version — An Assistant’s View of the Competition
- Malta Airport Gives Schengen a Slap in the Face
- Officially Selected for the X-Pyr 2014 Competition to Cross the Pyrenees by Paraglider
- A Scuba Diver Never Loses His Stripes
- I’ve Reached Middle Age, or so they say, welcome to the Fabulous Forty (40)
- Dubai Residency Visa: Medical & Blood Tests are a Waste of Time
- Pay-to-Volunteers: A Sad State of Affairs in Africa
- Malaria: Arguably the only African natural resource unwanted by the rest of the world
- Still No Conclusive Evidence Suggesting Syrian Government Used Chemical Weapons
- Will it take one million casualties in Syria before the West gets involved?
- Taking Advantage of Idiosyncrasies and Body Language during Business Meetings and Difficult Situations
- Dubai Holds Great Earning Potential for Anglophone East-Africans
- Absence Makes The Heart Grow Fonder — Does it Really?
- Five Thousand Eight Hundred and Sixty-Two Kilometres from Home
- Avoiding Chronic Short-term Memory Loss on Large Projects
- Invited to Talk about Achieving Enjoyment at Work
