Biometric Hype: A Risky Proposition for Fingerprint and Iris Scanners
August 3, 2016 Shem Radzikowski Comments Off on Biometric Hype: A Risky Proposition for Fingerprint and Iris Scanners

These days biometric sensors are part of just about every portable device. Fingerprint scanners are commonplace on laptops, phones and tablets. And with low cost iris scanners gaining popularity, we are likely to see more biometric tech in consumer-grade equipment. But for all their convenience, they aren’t as safe and robust as you’re being led to believe.
Sure, passwords are cumbersome and annoying Remembering complex ones isn’t everybody’s idea of a good user experience. Passwords have gotten a lot of bad press but they are still one of the strongest and most economical forms of protection we have when used appropriately.
Prolific Centralization of Biometric Data
I guess it depends on where you’re travelling, but a vast majority of my overseas trips, particularly in Africa and the Middle East, have required me to scan my fingerprints at immigration. This means that the country into which I’ve entered has now a record of my biometric data stored on their systems. It’s something we’ve grown accustomed to but until recently this type of treatment was reserved only for criminals.
If you’re the owner of an e-ID or e-Passport, chances are that the embedded chip contains your biometric modalities, such as fingerprint, photo or iris. Similarly, if you’ve ever been tagged in a photo on social media, it is more than likely that your facial biometric data is known in the public domain — think Facebook or LinkedIn.
The Samsung Galaxy Note 7 for example, with its integrated iris scanner, shoots out a beam of infrared light to detect and authenticate the iris. “Samsung says it’s impossible for the sensor to be fooled by high-resolution images of your iris” because the infrared signature would be different.[1] Whether it’s impossible to circumvent or not remains to be seen — no pun intended — time will tell.
Compromized Biometric Data
Now ask yourself, if some organization has access to all of your biometric data, be it Facebook or a Government, how safe is your data? And how confident are you that your biometric data isn’t shared between various parties? While biometric authentication is convenient and quick, it does create a massive security risk for anyone who relies on it as their only means of authentication.
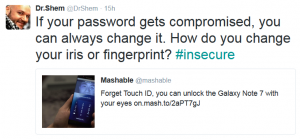
Within PKI, we have the ability to revoke compromized certificates. Similarly, when a password is lost or stolen, all that’s required to reestablish security is a password reset. In both these instances the process is relatively simple and well understood.
The question we should be asking is: how does a person revoke or reset their biometric data? At present, this is not possible. You only have two eyes, ten fingers and one face. Short of plastic surgery, once compromized, there is no way to reset any of your bio-features.
Conclusion
I’m not a big fan of mass biometric data collection, and the trend is worrying me. Private biometric usage on a private device is perfectly acceptable when paired with secondary authentication method, such as a boot/encryption pin or password. However, entrusting your biometric data to a commercial entity is just silly. You’re unlikely to ever know whether (and with whom) your biometric data is being shared.
Furthermore, the fact that your e-ID or e-Passport contains some biometric data, it is fair to say the government (and social media) has access to it too. Assume that all of your biometric data is already known. Remember, fingerprints and iris scans can always be taken without your permission or under duress.[2] Good luck trying to pry a password out of my brain.
Footnotes
- In addition to its Knox mobile enterprise security software and the fingerprint sensor embedded into the home button, the Note 7 has the world’s first iris scanning sensor. ^
- Because the constitutional protection of the Fifth Amendment, which guarantees that “no person shall be compelled in any criminal case to be a witness against himself,” may not apply when it comes to biometric-based fingerprints (things that reflect who we are) as opposed to memory-based passwords and PINs (things we need to know and remember). ^
References
Related
Subscribe
Subscribe and receive email notifications the moment Dr.Shem publishes a new post.
Our Sponsors
Recent Posts
- Dublin’s Breaking Point: Riots Expose Ireland’s Immigration Crisis
- Ireland’s Immigration Crisis: A Nation Overwhelmed
- My Journey with Ropes: Scaling New Heights
- Climbing Mountains in and Around Pokhara: An Adventure Beyond the Summits
- A Nomad’s Notebook: Charting My Path Across Continents
- From Pierogi to Pavlova: My Transcontinental Childhood
- Riding Through History: A Personal Journey on the Irish Rail System
- Above the Azure: Discovering the Thrills of Paragliding in Malta
- Immersed in Nature: A First-hand Experience of Hiking in Wicklow
- My Emerald Isle: Why Ireland is the Epitome of Home
- Life in Boulder Colorado: A Quick Guide to Boulderites’ Lifestyle, Culture, and Values
- Rekindling a 25-Year-Old Friendship: A Journey Through Time
- The Spirit of Ireland: A Brief History of Irish Whiskey
- Comparison of Firearm Purchase Procedures in California vs Texas
- First impressions on Austin, Texas and its Tech Scene
- Buying a Gun in California – Not as Easy as it Sounds
- Biometric Hype: A Risky Proposition for Fingerprint and Iris Scanners
- Temple Bar: A Great Place to Live, for the Deaf Insomniacs
- Zero Trust and The Mutating Threat Landscape
- CyberSecurity: Expanded Look at the APT Life Cycle and Mitigation
- Mentors: The Priceless Few and Lessons Learned
- Selected by Hackin9 and eForensics Magazines as a Contributing Cybersecurity Expert
- Notes from the Cloud Security Alliance (CSA) Congress EMEA 2015
- Analyzing the Power Consumption of Mobile Antivirus Software on Android Devices
- Poorly Configured Proxies Leaking Information through “X-Forwarded” and “Via” HTTP Request Headers
- CyberSecurity: A Case Study of the Need for Change
- Cyberconfusion: Cyber Security, Cyber-Security or Cybersecurity?
- CyberSecurity: Origins of the Advanced Persistent Threat (APT)
- A Newcomer’s Take on Dublin Town — First Impressions
- Crypto Wars and Messaging: How Secure are Skype and WhatsApp?
- Reduced Cognitive Performance: Open-Plan Offices, Noise and Collaboration
- First Impressions on Working with Huawei’s European Research Center (ERC)
- Lessons I’ve Learnt from various Relationships
- Money and Friends Don’t Always Mix
- X-Pyr 2014: My Annotated Version — An Assistant’s View of the Competition
- Malta Airport Gives Schengen a Slap in the Face
- Officially Selected for the X-Pyr 2014 Competition to Cross the Pyrenees by Paraglider
- A Scuba Diver Never Loses His Stripes
- I’ve Reached Middle Age, or so they say, welcome to the Fabulous Forty (40)
- Dubai Residency Visa: Medical & Blood Tests are a Waste of Time
- Pay-to-Volunteers: A Sad State of Affairs in Africa
- Malaria: Arguably the only African natural resource unwanted by the rest of the world
- Still No Conclusive Evidence Suggesting Syrian Government Used Chemical Weapons
- Will it take one million casualties in Syria before the West gets involved?
- Taking Advantage of Idiosyncrasies and Body Language during Business Meetings and Difficult Situations
- Dubai Holds Great Earning Potential for Anglophone East-Africans
- Absence Makes The Heart Grow Fonder — Does it Really?
- Five Thousand Eight Hundred and Sixty-Two Kilometres from Home
- Avoiding Chronic Short-term Memory Loss on Large Projects
- Invited to Talk about Achieving Enjoyment at Work